73deb40: A Complete Guide to Understanding This Unique Identifier
When you come across a code like 73deb40, you might wonder what it represents and why it matters. This alphanumeric string appears in various digital contexts, from software development to data tracking systems. Understanding these identifiers helps you navigate the technical landscape more effectively.
What Is 73deb40?
The code 73deb40 is a hexadecimal identifier commonly used in version control systems, database references, and digital tracking mechanisms. Hexadecimal codes like this one contain numbers (0-9) and letters (a-f), creating a compact way to represent large amounts of information.
In most cases, you’ll encounter this type of identifier in:
- Git commit hashes that track code changes
- Database entry references
- Transaction IDs in blockchain systems
- Session tokens for web applications
- File checksums for verification
The structure follows a specific pattern that computers can process quickly while remaining relatively short for human reference.
Why These Identifiers Matter
Digital systems need reliable ways to track and reference information. Using sequential numbers (1, 2, 3) works for small datasets but breaks down at scale. Hexadecimal identifiers solve several problems at once.
Uniqueness at Scale
When millions of transactions happen simultaneously, you need identifiers that won’t collide. The hexadecimal system provides enough combinations to make duplicates virtually impossible within a given system.
Compact Storage
Seven characters can represent over 268 million unique values. This efficiency matters when you’re storing billions of records and every byte counts.
System Compatibility
Hexadecimal works across different programming languages and platforms without translation issues. A code like 73deb40 means the same thing whether you’re using Python, JavaScript, or any other language.
How These Codes Work
The hexadecimal system uses base-16 instead of the base-10 decimal system you use in everyday life. Each position can hold 16 different values (0-9 and a-f).
Breaking down 73deb40:
- 7 represents the value seven
- 3 represents three
- d represents thirteen (in decimal)
- e represents fourteen
- b represents eleven
- 4 represents four
- 0 represents zero
When converted to decimal, this specific code equals 121,393,984. But most systems keep it in hexadecimal form because it’s more compact and easier for developers to work with.
Generation Methods
Systems typically create these identifiers through:
- Hashing algorithms that convert input data into fixed-length codes
- Random number generators with hexadecimal output
- Sequential counters displayed in hexadecimal format
- Timestamp-based algorithms that ensure uniqueness
The method depends on the specific application and requirements for collision resistance.
Who Uses These Identifiers
Different professionals interact with hexadecimal codes regularly, though most end users never see them directly.
Software Developers
Programmers work with these codes daily when tracking changes in version control systems. Every time code gets saved to a repository, it receives a unique hash for reference.
Database Administrators
DBAs use hexadecimal identifiers to manage records efficiently. These codes help maintain referential integrity across complex database structures.
Cybersecurity Experts
Security professionals rely on hexadecimal hashes to verify file integrity and detect tampering. Comparing hash values quickly reveals whether data has been modified.
Blockchain Engineers
Cryptocurrency and blockchain systems use hexadecimal extensively for transaction IDs, wallet addresses, and block identifiers.
Similar to how influencers gone wild tracks viral moments across social media, these identifiers track digital events across technical systems.
Tips for Working with Hexadecimal Codes
Understanding these identifiers becomes easier with practice. Here are practical approaches that help:
Use Conversion Tools
Online calculators instantly convert between hexadecimal and decimal. This helps when you need to understand the magnitude of a value or perform calculations.
Recognize Patterns
After seeing enough examples, you’ll start recognizing valid hexadecimal strings. Invalid characters (like ‘g’ or ‘z’) immediately stand out.
Keep Reference Documents
Maintain a list of important identifiers for your projects. This saves time when you need to reference specific commits, records, or transactions.
Implement Verification
Always verify codes before using them in production systems. One wrong character can point to completely different data.
Understand Context
The same hexadecimal string might mean different things in different systems. Always confirm what system generated the code and what it represents.
Tricks That Save Time
Experienced professionals develop shortcuts for working efficiently with these codes.
Partial Matching
Most systems let you reference identifiers using just the first few characters. Instead of typing all of 73deb40, you might only need 73deb if it uniquely identifies the item.
Copy-Paste Safety
When copying these codes, include a character before and after, then trim. This prevents accidentally missing the first or last character.
Checksum Validation
Some systems include built-in validation. Learn the checksum algorithm for your system to catch errors before they cause problems.
Search Integration
Set up your development environment to search for hexadecimal patterns. This helps locate references across large codebases quickly.
Review of Common Applications
Different industries apply hexadecimal identifiers in specialized ways.
Version Control Systems
Git generates a 40-character SHA-1 hash for every commit. While 73deb40 is only seven characters, it might represent a shortened version of a longer hash. Developers reference these constantly when reviewing code history, merging branches, or reverting changes.
Database Management
Modern databases often use hexadecimal for primary keys, especially in distributed systems. This approach avoids conflicts when multiple databases sync their records.
Web Development
Session IDs and authentication tokens frequently use hexadecimal encoding. This helps prevent prediction attacks where malicious actors try to guess valid session codes.
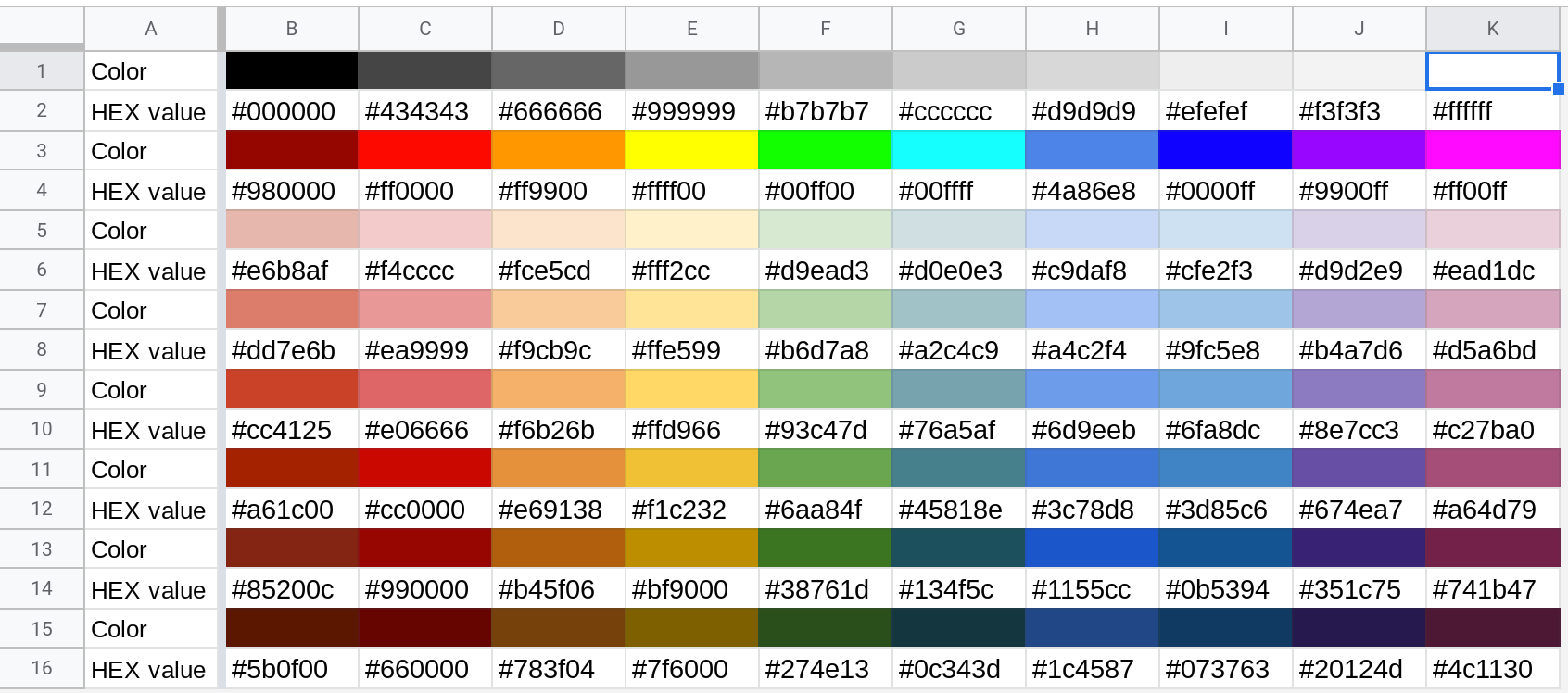
Color Codes
Web designers work with hexadecimal color codes daily. While 73deb40 could theoretically represent a color (a muted teal-gray), most color codes use six characters preceded by a hash symbol.
Pros and Cons
Like any technical approach, hexadecimal identifiers come with trade-offs.
Advantages
- Extremely low collision probability in properly designed systems
- Compact representation saves storage space
- Universal compatibility across platforms and languages
- Easy for computers to process and compare
- No sequential pattern that attackers can exploit
Disadvantages
- Not human-readable without conversion
- Easy to transcribe incorrectly
- Difficult to remember compared to meaningful names
- Requires tools for conversion and validation
- Can confuse non-technical stakeholders
Benefits for Your Projects
Implementing hexadecimal identifiers strategically improves system performance and reliability.
Scalability
As your application grows, these codes continue working without modification. You won’t hit limits that force database restructuring.
Security
Non-sequential identifiers prevent enumeration attacks where hackers systematically try consecutive values to access resources.
Distribution
Multiple servers can generate identifiers independently without coordination, enabling truly distributed systems.
Debugging
Unique identifiers make tracking issues through complex systems much easier. You can follow a single transaction across multiple services.
Important Facts
Some technical details help you work more effectively with these codes.
Character Set
Valid hexadecimal uses only: 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, a, b, c, d, e, f. Any other character indicates an error or different encoding.
Case Sensitivity
Hexadecimal is typically case-insensitive. Both 73DEB40 and 73deb40 represent the same value, though lowercase is conventional.
Length Variations
Different systems use different lengths. Git uses 40 characters, while other systems might use 8, 16, or 32. The length determines how many unique values are possible.
Leading Zeros
Some systems preserve leading zeros (0073deb40) while others drop them (73deb40). Know your system’s behavior to avoid confusion.
Risks to Watch For
Working with hexadecimal identifiers requires attention to potential problems.
Truncation Errors
Copying partial codes can reference the wrong item if multiple entries share the same prefix. Always verify you have enough characters for unique identification.
System Assumptions
Don’t assume identifiers work the same across different platforms. What works in one database might fail in another.
Manual Entry Mistakes
Typing these codes manually introduces errors. Always copy-paste when possible and implement validation checks.
Legacy System Issues
Older systems might have shorter identifiers with higher collision risk. Plan for migration if you’re scaling up.
Opportunities for Implementation
Strategic use of hexadecimal identifiers opens new possibilities.
API Development
Use these codes for resource URLs in RESTful APIs. They’re cleaner than exposing internal database IDs and prevent information leakage about record counts.
Audit Trails
Every system action can receive a unique identifier for tracking. This creates comprehensive audit logs for compliance and debugging.
Microservices Architecture
Distributed systems benefit from globally unique identifiers. Each service can generate codes independently while avoiding conflicts.
User-Facing Features
Order tracking, support tickets, and confirmation codes all work well with shortened hexadecimal values. They’re short enough to communicate verbally while remaining unique.
Features That Stand Out
Modern implementations of hexadecimal identifiers include helpful features.
Collision Detection
Advanced systems check for duplicates before assigning identifiers. This adds a safety layer even though collisions are statistically unlikely.
Timestamp Embedding
Some algorithms encode creation time within the identifier. This allows sorting by age without accessing the full record.
Custom Alphabets
While standard hexadecimal uses 0-9 and a-f, some systems create custom alphabets that exclude confusing characters like 0 and O or 1 and l.
Checksum Digits
Adding a verification digit helps catch transcription errors. The system can validate the code structure before looking it up.
Performance Considerations
How you implement these identifiers affects system speed and efficiency.
Indexing Strategy
Database indexes on hexadecimal fields perform differently than numeric indexes. Choose the right index type for your database engine.
String vs Binary Storage
Storing hexadecimal as strings uses more space than binary representation. Convert appropriately based on your needs.
Comparison Speed
Hexadecimal comparisons are fast, but longer codes take more time. Balance uniqueness requirements against performance needs.
Memory Usage
Each character requires storage. In systems with billions of records, this adds up. Optimize length based on actual uniqueness requirements.
Scam Alerts
Be cautious when dealing with hexadecimal codes in certain contexts.
Fake Transaction IDs
Scammers sometimes provide fake hexadecimal transaction IDs to appear legitimate. Always verify through official channels.
Phishing Attempts
Emails claiming to reference specific codes might be phishing attempts. Don’t click links based solely on an identifier that looks valid.
Impersonation
Someone could claim a legitimate code belongs to them. Verify ownership through proper authentication, not just code possession.
Reports and Documentation
Proper documentation makes working with these identifiers much easier.
Naming Conventions
Establish clear naming for what different types of codes represent. Is it a transaction ID, session token, or commit hash?
Reference Guides
Create quick-reference documents showing code formats and where to find them in your systems.
Change Logs
Track when you modify identifier generation algorithms. This helps diagnose issues with codes created during specific periods.
Training Materials
New team members need clear explanations of how your organization uses these codes and what they mean.
Platform Mission
Systems using hexadecimal identifiers aim to provide reliable, scalable, and secure data management. The technical implementation serves broader goals of system integrity and user trust.
Organizations implementing these codes properly demonstrate attention to technical excellence. They’ve thought through scalability, security, and long-term maintenance rather than taking shortcuts.
When you see a well-implemented identifier system, it reflects an engineering culture that values doing things right even when users never see the details.
Moving Forward
Understanding codes like 73deb40 helps you work more effectively with modern digital systems. Whether you’re a developer building applications, an analyst tracking data, or a professional working with technical systems, this knowledge proves valuable.
Start by recognizing these codes when you encounter them. Learn what they represent in your specific context. Then explore how you might implement them to solve problems in your own work.
The hexadecimal system has proven itself over decades of use. It balances human usability with computer efficiency better than most alternatives. As systems grow more complex and distributed, these identifiers become even more essential for maintaining order and reliability.
Take time to understand the identifiers in systems you use regularly. Ask questions about their purpose and implementation. This knowledge compounds over time, making you more effective at navigating technical environments and solving complex problems.